Try our vulnerability management service free for 7 Days, covering up to 10 systems. Discover how we identify, prioritize, and mitigate vulnerabilities effectively—at no cost or obligation.
Network Scan Findings: Identify potential network-based threats swiftly and deliver timely, actionable insights to bolster your security measures.
Detailed Inventory: Compile a comprehensive inventory of Applications, Extensions, Ports, Services, Interfaces, Vulnerabilities, and more, for a full understanding of your client’s digital landscape.
Automated Continuous Scanning and Remediation: Stay one step ahead of threat actors across all operating systems, Windows, Linux, Darwin, and ARM.
Missing Patches and Updates Identification: Equip your business to identify missing patches and updates in Microsoft Windows and third-party applications.
Support Over 600 Third-Party Applications: Leave nothing to chance with support for whatever software your clients use.
View Missing Patches: Quickly identify missing OS patches and security updates for both Windows and Mac systems.
Automate Remediation: Set schedules or policies for automatic patch installation, reducing manual efforts and ensuring consistent protection.
Role-Specific Reports: Access reports tailored to the different needs of Executives, Supervisors, and Engineers, all available for download.
Various Format Options: Select your preferred report format for download: PDF, Word, Excel, or PowerPoint.
![]() 1. Comprehensive Asset Management: Includes inventory of all devices (PCs, servers, and external assets), identification of deprecated assets, and tracking of pending OS patches. Tools like attack surface mappers and application baselines enhance asset visibility.
1. Comprehensive Asset Management: Includes inventory of all devices (PCs, servers, and external assets), identification of deprecated assets, and tracking of pending OS patches. Tools like attack surface mappers and application baselines enhance asset visibility.
![]() 2. Detailed Vulnerability Assessment: Identifies and categorizes application and operating system vulnerabilities, highlights network scan findings, and prioritizes vulnerabilities based on severity for efficient remediation.
2. Detailed Vulnerability Assessment: Identifies and categorizes application and operating system vulnerabilities, highlights network scan findings, and prioritizes vulnerabilities based on severity for efficient remediation.
![]() (3.) Compliance Monitoring and Reporting: Ensures adherence to standards such as PCI DSS, HIPAA, NIST, and GDPR with automated assessments, compliance checks, and detailed compliance-specific reports for audits.
(3.) Compliance Monitoring and Reporting: Ensures adherence to standards such as PCI DSS, HIPAA, NIST, and GDPR with automated assessments, compliance checks, and detailed compliance-specific reports for audits.
![]() (4.) Active Directory (AD) Security: Includes AD problem detection, detailed audits, Microsoft Entra ID integration, Secure Score evaluations, and security inspection reports to enhance AD security posture.
(4.) Active Directory (AD) Security: Includes AD problem detection, detailed audits, Microsoft Entra ID integration, Secure Score evaluations, and security inspection reports to enhance AD security posture.
![]() (5.) Patch Management: Tracks and deploys critical patches for applications and operating systems, with automated scheduling to ensure timely updates without disrupting operations.
(5.) Patch Management: Tracks and deploys critical patches for applications and operating systems, with automated scheduling to ensure timely updates without disrupting operations.
![]() (6.) Personal Identifiable Information (PII) Protection: Monitors and secures PII through setup of alerts and tracking systems to prevent unauthorized access or data breaches.
(6.) Personal Identifiable Information (PII) Protection: Monitors and secures PII through setup of alerts and tracking systems to prevent unauthorized access or data breaches.
![]() (7.) Customizable Reporting: Provides advanced report generation tools, offering insights in various formats (PDF, Excel, Word) on vulnerabilities, compliance, AD audits, and more.
(7.) Customizable Reporting: Provides advanced report generation tools, offering insights in various formats (PDF, Excel, Word) on vulnerabilities, compliance, AD audits, and more.
![]() (8.) Firewall Management: Includes configuration reviews, rule updates, and integration with external scan findings to reduce attack vectors.
(8.) Firewall Management: Includes configuration reviews, rule updates, and integration with external scan findings to reduce attack vectors.
![]() (.9) Attack Surface Reduction: Uses tools like attack surface mappers and vulnerability prioritization to minimize exposure to threats and strengthen overall security.
(.9) Attack Surface Reduction: Uses tools like attack surface mappers and vulnerability prioritization to minimize exposure to threats and strengthen overall security.
![]() (10.) Risk-Based Approach: Focuses on identifying, assessing, and mitigating risks based on their potential impact, aligning resources effectively to address critical vulnerabilities.
(10.) Risk-Based Approach: Focuses on identifying, assessing, and mitigating risks based on their potential impact, aligning resources effectively to address critical vulnerabilities.
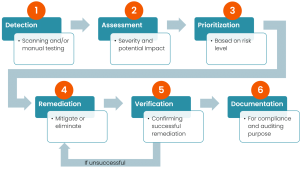
Vulnerability scanning is an inspection of the potential points of exploit on a computer or network to identify security holes. A vulnerability scan detects and classifies system weaknesses in computers, networks and ...
we perform a thorough verification process before deploying any patches or updates. This includes checking the file hashes to ensure the integrity and authenticity of the downloaded files and checksum validations. Deployment is both manual and automated.
We support some of the common cyber security compliance standards scans that help to form a strong basis for a good cybersecurity strategy. Scanning for Compliance standards like PCI DSS, HIPAA, GDPR IV, NIST 800-53, NIST 800-171, CIS, CIS 8.0, ISO 27002, and Essential Eight is supported with ...
All assets, firewalls and other assets including software inventory. Assets are added and Monitors are added automatically based on the type of asset added, problems, solutions, external assets, depreciated assets and individual asset health report.
Personally identifiable information (PII) is information that, when used alone or with other relevant data, can identify an individual.We scan for PII and let you know where they exist on your network.
View all certificates found during external scanning jobs across companies with key information about the certificates. This includes Company Name, Asset Name, IP, Port, Issuer, Not Valid After, Not Valid Before, SSL Expired Status...